Individual algorithm-based multi-factor authentication (dopeIN®)
dopeIN® is the patented method for
individual algorithm-based multi-factor authentication
(MFA) (Patent DE 10 2021 125 572 —
DPMA +
Google Patents).
In the patent, “dopeIN” is used as the short name for this method.
Core principle: Instead of entering a secret code 1:1, the input is the result of a dynamic task whose solution path the user has defined in advance.
People are the decisive security factor with dopeIN® - the first encryption begins with the user himself!
Authentication processes are becoming increasingly mechanised: Machines communicate with each other, humans only execute.
With dopeIN®, people, with their unique skills and experience, once again become the decisive link in the communication chain between humans and machines. With dopeIN®, the encryption of information starts with the user.


For this purpose, passwords, PINs or codes are no longer entered directly, one-to-one, in processes protected with dopeIN®. The input is the result of a dynamic task. The user has previously defined this task and its solution himself. The complexity of the authentication can be adjusted according to the individual security requirements and personal experience of each user.
dopeIN® is a patent. The method is integrated into existing systems.
dopeIN® is based on patent DE 10 2021 125 572 (DPMA + Google Patents) — "Method for performing an authentication process by an individual system user". dopeIN® is a method, not a product. To use dopeIN®, it is integrated into an (existing) security system.
Basic principle: Implementation phase and application phase
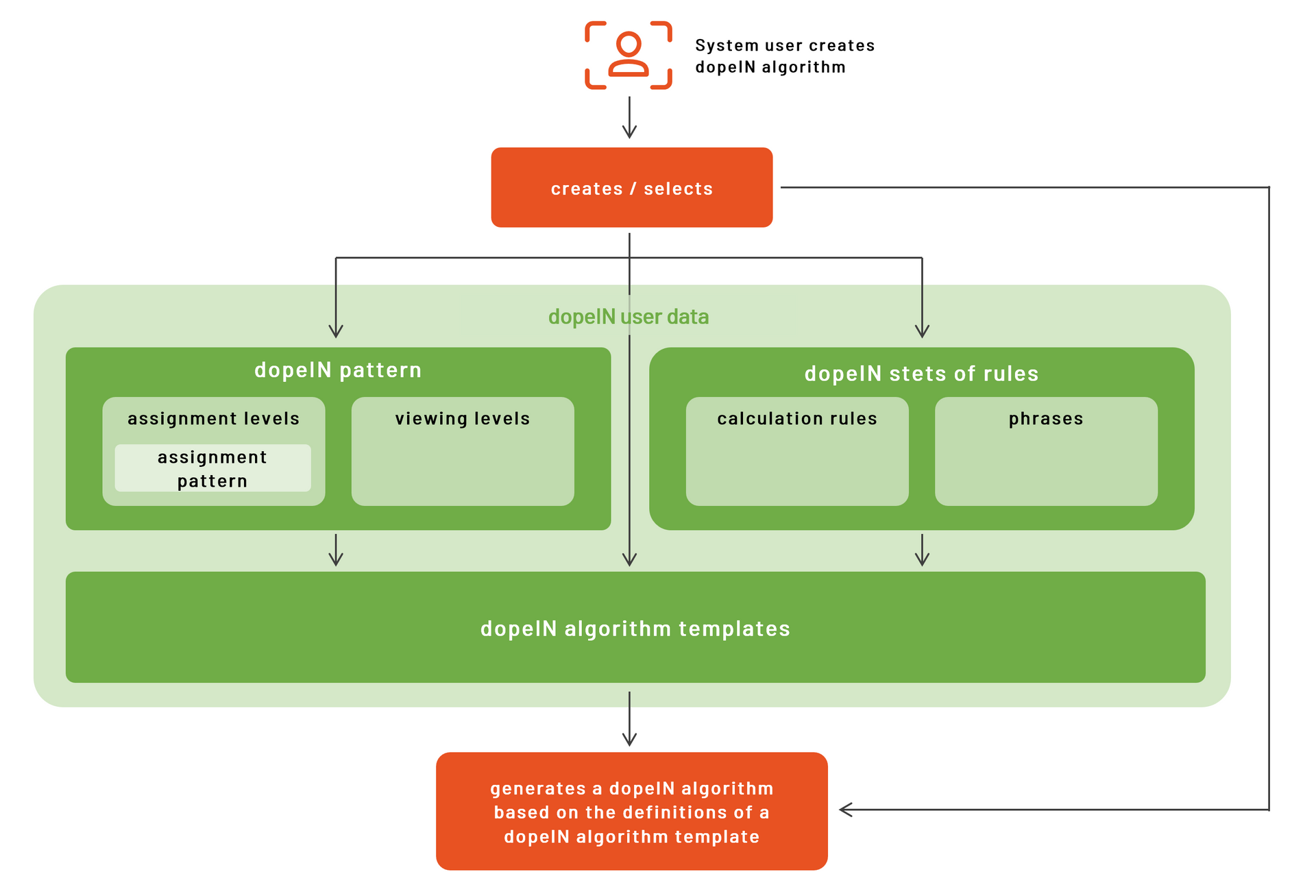
The dopeIN method consists of two phases: the creation of an algorithm (implementation phase) and the execution of authentication (application phase).

In the implementation phase, the
user creates their own
customised algorithm.
In the application phase, the
user's individual algorithm is
executed.
In the implementation phase, users first define their individual rules for human-machine communication. Users have a wide range of options for this, such as the use of calculation rules, patterns, phrases, viewing levels, etc. Users then compile their individual algorithm from the selected security fragments. In the application phase, users execute their algorithm for concrete application. When queried by the machines, they draw on their experience.
In both phases, users do not need any specialised knowledge of cryptography, computer science or mechanics. dopeIN® does not require the storage of sensitive personal data, in particular biometric information (e.g. fingerprint, facial recognition, iris scan).
This changes when you use dopeIN®: Individualisation and dynamisation speed up and improve the security of authentication.
In conventional authentication procedures, the role of humans is increasingly being reduced to execution. Machines take over the actual security communication. This is intended to relieve the burden on humans and speed up processes. However, the potential of security fragments is not fully utilised. In times of increasing cybercrime, the use of AI and the up-and-coming quantum computing, however, all security potential should be systematically and proactively utilised!

static passwords
The properties of the input field and the password itself are static and cannot be individually personalised and/or dynamically adapted.
dopeIN® makes authentication procedures individually scalable and picks up users at their personal security expectations and experiences. Freedom of choice and user self-determination are the focus of dopeIN® and strengthen the role of people as a decisive security factor in authentication procedures. By consciously and systematically involving people in the authentication process, the first encryption stage is carried out by the user themselves. This exploits completely new security potential that can be easily integrated into any conventional authentication process.

dynamic passwords
With dopeIN®, the properties of security fragments are personalised and can be adapted individually and dynamically.




